Crypto security must be a priority for everyone involved with cryptos and the blockchain technology. Specially after the recent Twitter Hack that reminded us how active are the crypto-scammers and how creative they can be to get their hands on our hard-earned crypto assets.
The world of crypto coins is a booming sector that continues to grow year after year. More and more people are encouraged to invest in digital currencies to be able to make transactions on the Internet without depending on the physical money we have stored in the banks.
We never think that someone can enter a bank and steal all the money we have stored there, as they have strong security measures to protect their customers’ savings. Even today, most banks keep the money outside their premises, in places we do not know and that have a very high degree of security.
In the digital currency field crypto security is even more important because all our transactions pass through the internet and we are totally exposed to attacks from malicious people. Security for your crypts has to be the fundamental pillar when investing in crypto assets.
There is no point in going all out to buy and sell Bitcoin, Tron or Ethereum if we don’t pay attention to security.
The protection in our digital currency movements and transactions has to be very high to ensure that our decentralized currencies are not lost over the network. But before we go any deeper into the security of our crypts, it is worth remembering the meaning of crypto coins.
Contents
Basics and use of the Cryptos

Therefore, we can understand that this completely digital currency is an alternative value to the dollars or euros that we know and use daily. Adoption is growing and even some countries like India, Rusia, Dubai, Iran or Venezuela are creating their official state based cryptocurrencies.
Because of this, you might have some doubts and wonder why it is so interesting to get some Bitcoin, Ethereum, Tron or Ripple. The answer to that question is very straightforward, and that is that the principles linked to virtual currencies are very simple: their scarcity and the fact that only the person that owns the private keys can manage the cryptocurrencies. Decentralized blockchains give all the financial control to said private keys owner.
When a product is built from scratch in a gradual or limited way, there is usually a limit to the money supply. The meaning of all this is also very simple, and that is that the value of these digital currencies is destined for what we call hyperinflation. Finally, getting some crypts could be a smart investment for many people interested in this decentralized economy.
Common scams in cryptocurrencies
It becomes complicated to talk about the Internet without mentioning the scams that run daily, regardless of the field. Internet scams are everywhere and it is a very serious problem that affects many inexperienced people who fall into the nets of scammers. The most common scams that take place within the internet world are usually the following:
- Sending viruses through e-mails
- Gaining access to other people’s social networks without authorization
- Sending emails impersonating external identities to get your personal data
- Obtaining personal data through fictitious forms that look real

That’s why developing functional and updated crypto security to protect our digital currencies is tremendously important if we want to safeguard our investments and our savings.
How does a fraudster manage to breach security?
Computer hackers usually use some fairly simple but effective tricks to achieve their goals, which in most situations involve stealing our private keys or sending our cryptocurrencies to completely different addresses than we have decided. We’ll explain to you which methods are most commonly used by fraudsters.
Malicious mobile applications
This system has been widely used over the past few years by many fraudsters because it is usually difficult to detect the fraud being committed. They have the ability to publish commercial applications that use malicious code, and that to the end user may appear to be working properly. What these apps do is send your cryptos to a hacker’s account, making you think you are sending it to an official account.
In general, applications based on the Android operating system are more likely to receive this type of modification. It is important that you download applications only from official and trusted sources, otherwise you will be exposing yourself to installing a malicious application. It is also advisable to periodically clean up unused applications and install anti-malware on your mobile that can detect this type of app.
One method that everyone can use to protect your mobile device and increase your crypto security is to add double authentication (2FA) to your crypto applications. This way, only you will be able to run these applications and increase the protection of all your digital currencies.
Browser extensions
The use of extensions in our internet browsers has become a way to facilitate many tasks that we perform in them. But let’s not forget that extensions have the same problem as the applications we have mentioned in the previous point. They are prone to be modified to perform vandalism acts and scams.
These extensions can for example read everything you write in real time with a keylogger, so if you have a malicious extension installed, it could be reading your private key. The best advice for securing your crypts in this regard is not to download applications from unreliable sources.
Copy and paste
Generally, when we want to make a digital transaction using our cryptos, we look for the address of the account to which we want to send our cryptographic coins. We then copy that address and paste it into our wallet to proceed with the transaction.
This is the normal procedure, and should not be a problem under normal circumstances. However, here we find another of the great problems caused by computer scams that have as their sole objective the management of our digital capital.
CryptoShuffler is one of the most widely used programs for this type of digital abuse, which can violate the security of our cryptos. It is a small program that will change the address that we have previously copied for another one that has absolutely nothing to do with the one we had copied. This works with any kind of password and the use of these programs is very common.
First crypto security tip: Manually check the address of the destination account once it is pasted in the field of our wallet. You can also use the QR code for more security. Although the system of verifying the address seems very obvious, a large percentage of people do not do it, so they can easily fall into this type of vulnerability.
- Second crypto security tip: It is advisable not to install unknown software or software you do not trust, and it is also highly recommended to regularly use anti-malware software to clean your personal computer of malicious programs.
Cloned web pages
Many times the method of cloning websites is used in order to trick the user. Usually, the scammer’s website is called practically the same as the official site, just changing some letters to confuse the visitor. Once inside, the look is practically identical, so people will enter their personal data with complete confidence, without realizing that they are totally violating the security of their cryptocurrencies.
To avoid this, you should always verify that the website has the HTTPS certificate and double check that the name of the website corresponds exactly to the place you want to access. There are also applications such as Cryptonite that have a database with malicious websites, and when you access one of them it issues a warning highlighting the URL.
Fraudulent ICOs
An ICO is a financing instrument that it’s used to launch a new cryptocurrency to the market. It is comparable to a Crowdfunding. Entrepreneurs create a token, also called virtual currency or crypto-currency, to sell to investors in order to carry out a project.
Each of the different characteristics of ICOs, are described in their white paper, which has a developmental objective or purpose, but unfortunately not all of them are legitimate. Fraudulent ICOs have made their way into the crypto ecosystem to the extent that some people strongly believe that an ICO is a safe form of fraud, although this is not always the case of course.
The key to avoiding ICO scams is for everyone to do their research. We must be aware of the warning signs, put our heads together, consider the possible risks, and finally decide whether it is worth investing. An informed investor already has a lot to gain from improving his investment portfolio and acquiring long-term results; always keeping his crypto security measures on check.
Forged 2FA authentication
This security system is widely used and known today by many people. This service is based on the use of a second authentication factor to provide a greater crypto security layer. Thanks to this system, the protection is increased in a very remarkable way, since a second device (such as a mobile phone) is required to access the website or carry out the transactions through the wallet.
But some smart hackers can trick the phone companies to take control of your private number, so this system has to be treated with care, if something suspicious happens don’t hesitate in contacting your phone company to make sure that no third person can take control of your number.
Pishing through emails
Sending fraudulent e-mails is a method used for many years to carry out scammy actions, usually through impersonation. It is a system based on sending an e-mail using the exact appearance or very similar to that of a third party, such as a bank. The end user, upon receiving this email, believes that it is an official email and does not usually think that it may come from an electronic scam.
The design and appearance of the email is so similar and real, that many users enter their details in the url provided in that email without being aware that they are sending all their details to a person with bad intentions.
For these cases, it is recommended to be extremely cautious and to check the web address to which the links within those emails point. If you detect anything strange, we recommend that you directly delete that email.
Crypto security 101
Internet security is of vital importance today. Enhancing the security of our personal information, our cryptographic products and our personal information is very important, and even more so with the notable increase in cybercrime that is occurring in recent years.
Criminals seeking to take over our digital assets are using a huge set of tools aimed at scamming, including many types of viruses, ransomware, and malware. All of them aimed at attacking crypto security and diverting crypto currencies. But we must point out that these malicious tools are not designed exclusively to intercept users’ personal information.
As the popularity of crypto currencies has increased significantly over the last decade, cyber attacks on crypto users have also increased. Some crypto exchanges have also been attacked, compromising their security and that of their users.
Other instances, the use of fake wallets has caused many people to lose all their digital currencies. The moment users transfer their crypts to the fake wallet, those crypto currencies actually go into the fraudsters’ wallets.
Maintaining and storing your crypts safely at all times has to be imperative.
How do we keep our crypto currencies safe?
Store passwords in different places
The use of passwords to protect our wallets is a widely used, and generally quite effective, security method. Many times, when we create a wallet, a 24-word phrase is generated. This phrase is the seed to be able to recover your data in case of loss. This seed has to be managed very carefully in order not to suffer an accident and lose it in the future.
If you decide to protect that seed by writing it down on a piece of paper, it is advisable to make at least two copies and keep them in separate places.
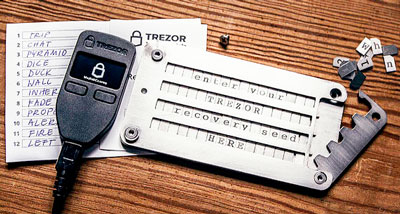
Memory cards are a great option for storage, but they tend to have limited durability and can be damaged relatively easily. It is convenient to use both digital and analog formats, some people even ingrave the phrases on steel as an extreme safety measure.
Use cold storage
When we talk about cold storage we are referring to a type of storage that does not require an internet connection. You can use a laptop by disabling its wifi connection or a desktop computer by removing the cable to the network card. Another option to consider is to use a hardware wallet, since they only use the internet when connected to the PC. Check our article about the best wallets to find the best for you.
Create complex and secure passwords
The passwords on our wallets are like the keys to our homes. The more complex they are, the harder it is for outsiders to get in. That is why, when creating a secure password for our cryptos, it is advisable to avoid all types of passwords based on our year of birth, name of our pets, song lyrics or consecutive numbers.
There is a type of software that is oriented to decipher passwords that a priori can seem complicated to guess. Therefore, it is convenient that you use a secure password generator or buy a hardware wallet in which you will have your crypts with a very high security. Some wallets have the option of entering several passwords, which helps to protect it very effectively.
Use two-factor authentication

Hackers usually stay away from accounts that have this protection system, as they prefer to try to discover the password of simpler accounts. When you enable the two-way authentication system anywhere, it is very important that you keep a copy of the secret code that will be used to activate 2FA in safe places.
Print the keys on paper
Protecting our keys and seeds is one of our goals in keeping our cryptos safe. One of the best systems is paper printing. Print different copies and place them in different protected places along with the paper wallets.
If you want more protection, you can print your secret keys on steel plates, minimizing much more their possible deterioration or destruction. You can buy a steel engraving tool and create your own plates as a backup of your passwords and seeds.
Caution
It may seem like a small thing, but it’s not. Prudence is an essential factor in avoiding potential pitfalls in the future. This means not bragging about how much you have earned from cryptographic currency, either among your friends or on social networks.
Not showing off your wallet to others to brag about how much crypt money you have is another security method you can apply to protect all your digital currencies.
The importance of backups
Creating backups to increase the security of our crypts is an extremely important factor. After having discussed the external agents that can endanger our digital currencies and the tips to keep them safe, it is also convenient to protect our private keys by backing them up. It is advisable to make several copies on a medium that is away from the usual place of work, but also to ensure that the storage place is secure and to protect the backup itself with appropriate encryption.
Performing different backups can help us in an excellent way against the deterioration, loss or theft of our data. Remember that this point is very important and should not be overlooked if you want the security of your crypts to be of the highest possible level.
Common mistakes in crypto security
It doesn’t matter if you are a cryptology professional or just a person who is curious about digital currencies, crypto security is an extremely important aspect to avoid problems in the future, which we often neglect or don’t pay enough attention to.
Protecting and securing the currencies we have has to be an imperative action if we value our money. And although we generally take minimal measures, we always make some mistakes that can be triggers for a malicious attack. Below, we explain the most common mistakes that are often made regarding the security of our crypto assets.
First mistake in crypto security
Not saving the data in a scrupulous way: If we use an online wallet, there is a great possibility that they will offer us a system to recover the password in case it is lost. If, on the other hand, we have our own hardware or software wallet and we lose our private passwords, we will have lost the possibility of recovering them in most cases. It is really our responsibility to save this data. And many people leave aside the aspect of keeping their private keys safe, thinking that they will never lose their access data.
This is a serious mistake, since many people lose their private passwords every year for not having saved them safely.
Second mistake in cryptocurrency security
Not using two-factor authentication: For many people, having to activate two-factor authentication is a big hassle, and the thought of having your mobile phone always at your side to access your crypts often seems a bit annoying. But when it comes to the world of crypts and security, activating the 2FA system is essential.
Some wallets have this method by default, but we have to use double authentication on all digital currency sites if we want to get the best security. Unfortunately, there are many people who aim to appropriate other people’s digital currencies, and when we lose our crypto currencies due to a cyber attack, there are no customer services that can solve this problem for us. Because of that, it is convenient to apply all possible security methods to guarantee our digital assets against malicious attacks.
We must be clear that although crypto currencies are digital assets, they are still money that belongs to us.
Third error on how to secure cryptocurrency

At the same time, they are places that can close down overnight, especially websites with a poor reputation or a security breach, and leave us without our money in a moment, practically without us noticing. Because of that, these “hot” wallets are great for storing small amounts of crypto currency for small purchases, but are not recommended for storing large amounts of our currency.
Keeping our crypts in cold hardware wallets is a fantastic option that very few people choose, where they can store our cryptomoney with great security being offline most of the time.
Fourth mistake
Using the public internet for transactions: To this day there are still a lot of people who connect to public networks to surf and operate the internet. We should never use the public Wi-Fi networks of hotels, airports, libraries, … to make transactions with our crypto currencies if we do not want to put them in danger. Such public networks often have large security holes in their systems due to their low protection for users.
Therefore, it is in our hands to avoid these types of connections to avoid getting scared with our digital money. If we need to make several transactions, the safest method is to make them from our private connection, and if we have an emergency, we can make them from our mobile phone connection. But never from a public network.
Fifth error
Not verifying our identity: On many online wallets or crypt exchange sites, they often allow you to create transactions without verifying your identity, which is often done by sending your personal identification documents. The requirements for trading our crypto currencies often differ from country to country, but serious and trusted sites often require identity verification before they can perform cryptographic transactions in order to improve security.

All these mistakes are very common and we usually overlook them thinking that we will never have problems with our accounts until the day comes when we get a major scare. Avoiding these mistakes can make the difference between having your crypts safe and secure or someone getting hold of our cryptographic coins.
If you want to avoid all those mistakes and increase your crypto security, go through them one by one to make sure you’re protecting your cryptos safely from possible cyber attacks.
Conclusions
As we have seen in this article on crypto security, there are many effective methods to keep our cryptocurrencies safe and secure from third parties. It is advisable to apply all possible methods to increase the security of our digital currencies.
Today there are many scams related to cryptomonies as it is a booming market and with a simple oversight you can run out of your coins. Computer hackers look for all possible methods to steal from people who do not pay enough attention to an aspect as important as security in their wallets, especially “hot” wallets, since they are constantly connected to the Internet.
Our advice for you to keep your cryptos safe at a very high level is to follow all the crypto security steps we have discussed in this article, paying attention to every step to activate all the protection methods. As we have seen, there are also many mistakes that are made by the little knowledge of some people and often just for convenience.
But the security of being able to keep your money safe is so important that we think that spending a minimum amount of time providing the best protection for your currencies has to be a priority.
Finally, remember that peace of mind when making online transactions using digital assets is a point that should be paramount for everyone. Danger is constantly lurking and scams happen every day, exposing thousands of accounts every day around the world.
Crypto security can be very effective by applying the tips we have explained above, or very fragile if you make the mistakes we have also explained. It is in your hands to provide the highest crypto security to your digital assets.




 First crypto security tip: Manually check the address of the destination account once it is pasted in the field of our wallet. You can also use the QR code for more security. Although the system of verifying the address seems very obvious, a large percentage of people do not do it, so they can easily fall into this type of vulnerability.
First crypto security tip: Manually check the address of the destination account once it is pasted in the field of our wallet. You can also use the QR code for more security. Although the system of verifying the address seems very obvious, a large percentage of people do not do it, so they can easily fall into this type of vulnerability.













Comments
No Comments